The usage of remote working tools such as Microsoft teams and Zoom has grown exponentially following the COVID-19 outbreak and subsequent government guidelines, for those of us who can, to work from home. And although working from home will help in curbing the spread of coronavirus, it also has the potential to leave some firms, who are doing their best to set up a healthy remote working setting for their employees, vulnerable to cyber security issues.
As your remote working tools improve, and the majority of your business communications move online, what will you need to put in place to protect your business from cyber threats?
Remote working cyber security checklist:
We’ve put together the below checklist to help you put the right measures in place to protect sensitive business data and get your remote team working seamlessly and safely over the coming weeks.
Do you have a working from home policy?
If, before the crisis, none of your staff worked from home, you may not have a specific working from home policy in place. It’s sensible to create a working from home policy if possible so that you can keep your staff and sensitive business data safe. Advise your employees on best practise use of computers and equipment at home for security purposes, such as keeping use of personal laptops to a minimum, and not storing files locally.
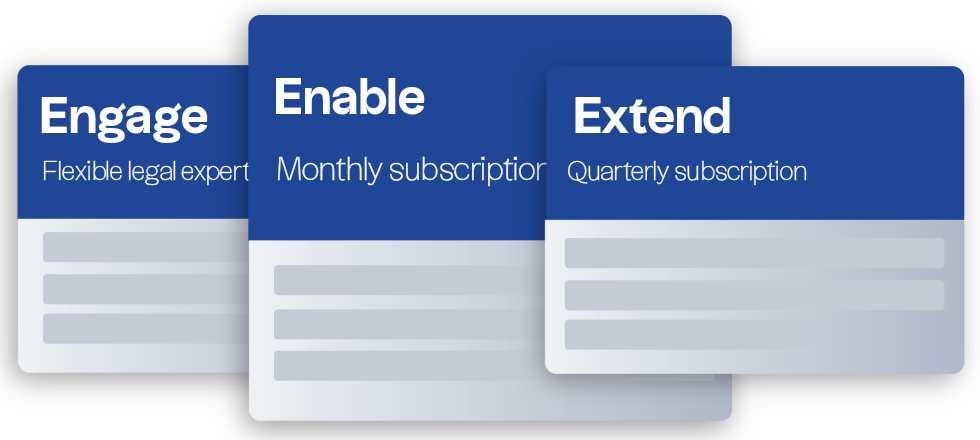
Access legal support from just £159 per hour
If you need support creating a working from home policy to reduce the risk of cyber threats while your staff are working from home, get in touch with our employment solicitors for advice.
We also have a team of specialist data protection solicitors in place to support businesses who may be concerned about managing risk at this time.
Do you know exactly what you need to protect?
If you don’t, now is the time to put a plan together with your IT services provider. Make sure they cover off all systems and devices that will be used remotely. That includes any BYOD devices that employees may be using – it’s important that any personal devices being used have the same level of security as those supplied by businesses.
Will service levels provided by your IT provider be reduced?
It’s worth checking with your IT provider on the updated process they will be using to provide support for those in your workforce who may be working from home. Think about how issues will be reported to your IT support, and whether this will continue as it did before the crisis. Will you employees be able contact your IT service provider directly for support? Or is there a need for a new system to be put into place to make sure remote workers can continue to work efficiently.
Have you activated all anti-virus and firewall products necessary?
Whether you’re a small or large firm this should be a priority for all computers, laptops and devices that leave your premises to support your remote workers over the coming weeks. If budget is an issue, research reliable, free anti-virus and malware tools that will give you the level of protection you need. Where your IT support systems already have this in place, make sure that all employees have this activated and correctly set up on their devices. It’s a simple step. But by sending out a reminder email to all staff to check this remotely, you will be putting the right protective measures in place and gain peace of mind.
Is all business-critical data being sufficiently backed up?
For smaller firms this may be as simple as backing up your data to a large external hard drive, but for those businesses who require masses of data to operate, it’s a good idea to leverage the protection that cloud storage can provide. Cloud storage security such as advanced firewalls, activity logging, encryption and intrusion detection will stand you in good stead when it comes to storing data, wherever you and your employees are working. Make sure all employees are educated on the proper use of your cloud storage systems -that way, there will be less chance of missteps that could leave you vulnerable.
Do you need to use a VPN to protect sensitive data?
If your business frequently handles particularly sensitive data, it may be wise for your staff to access this data via a VPN. This will add an additional layer of security for your business, scrambling login details, email communications, downloads and portals or sites you access so that hackers are less able to intercept this kind of information. For those with concerns about the security of their workforce’s data as they work from home, investing in a VPN package may help give you peace of mind while practically strengthening your security measures.
How secure is each of your employees wi-fi networks?
Remember that if your employees are accessing sensitive data while working remotely, the wi-fi networks they’re using may not have the same levels of protection, such as firewalls, as those installed in the workplace. If they’re working from home then it’s likely that they’re home wi-fi network is secured but if, while under self-isolation, an employee is using an open network, this could leave you vulnerable to a data breach or a malicious party intercepting sensitive data. Regular communication with your employees as to their whereabouts and their remote-working setup should tell you whether they will be vulnerable or not.
Have you advised your employees on opportunistic phishing emails?
Stay alert to continuous updates on potential cyber security vulnerabilities that your business could face as your teams work remotely over the coming weeks. You can get advice on phishing attacks in relation to the spread of coronavirus on the National Cyber Security Centre website – this may go some way to preventing your employees from falling into these traps and jeopardising the efforts your teams are currently showing to continue as efficiently and as routinely as possible.
Do you have measures in place to deal with a cyber attack, should one occur?
Your incident response plans may have been created without the current circumstances in mind. And while working outside of the everyday norm, it’s worth making sure that other response methods are put in place should an incident occur. For example, where you would normally have technicians physically intervene to reimage devices, you may instead want to test-run remote tools so that the relevant technicians can responds just as quickly as they would if they were on site.
Even if you have thorough cyber security measures already in place, it’s prudent to review your current policies to make sure you’re in a healthy position to handle the current disruption to routine working procedures. Where possible, get support from your IT service provider and keep your employees in the loop to stem any risk to your security.