Cyber attacks hit organisations of every size and the fallout - fines, downtime and lost trust - can dwarf the cost of prevention. A structured cyber-security risk assessment is the quickest way to spot weak points in your own systems and across your supply chain, then focus budget on the fixes that matter most.
This short guide walks CEOs, IT leads and in-house counsel through a practical, repeatable process: setting clear objectives, mapping assets and data flows, rating threats and vulnerabilities, and translating the results into actions that satisfy the UK GDPR security and accountability principles.
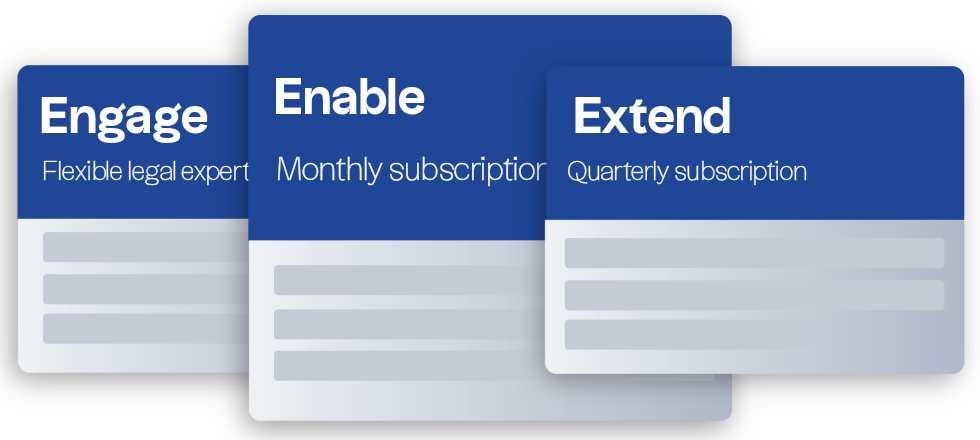
Need help turning the checklist into policy or evidence for regulators and clients? Our data protection solicitors can review your current controls, draft assessment templates and advise on risk-based priorities so you can strengthen defences with confidence.
We will look at the following:
Why are cyber security risk assessments important?
Cyber security risk assessments can help you meet regulatory requirements but also safeguard your business from big threats. These assessments will help you identify vulnerabilities in your systems and processes and ensure that you can respond effectively to potential cyber attacks.
By conducting these assessments regularly, you can continuously improve your security posture. This allows you to not only strengthen your defences against emerging threats but also optimise your security investments by focusing on the most critical vulnerabilities and eliminating unnecessary measures.
If your business falls under the UK General Data Protection Regulation (UK GDPR) law rules, you must ensure you process personal data securely and have measures in place to protect it from risk. This often requires implementing robust measures to protect data from unauthorised access or accidental loss. The UK GDPR’s ‘security principle’ is fundamental, and its ‘accountability principle’ obliges you to demonstrate your steps towards compliance.
Managing cyber security risks and conducting regular assessments is a critical component of GDPR compliance. These assessments help your business protect personal data and demonstrate accountability by:
- Identifying potential risks to the security of personal data.
- Implementing appropriate measures to mitigate these risks.
- Documenting your proactive approach to data protection.
In addition to the requirements under the UK GDPR, your business might also need to conduct cyber security risk assessments to comply with other obligations, such as industry-specific regulations or specific contractual agreements with customers.
What does a cyber security risk assessment involve?
A cyber security risk assessment involves a comprehensive review of your organisation’s security measures. It’s an opportunity to assess your current security measures, identify gaps, and determine how best to address them. It's sensible to involve senior management in the cyber security risk assessment process to ensure that the assessment aligns with your business's strategic objectives and receives the necessary resources and attention for effective implementation.
Without regular assessments, you might miss critical areas where your security needs improvement, which could leave your organisation vulnerable to cyber threats. Regular assessments can also help you streamline your security measures, making your efforts more cost-effective.
Regularly reviewing and updating your cyber security policies and procedures is crucial. This will help make sure that your organisation stays resilient against evolving cyber threats.
It’s important to understand that while cyber risk assessments are important, they are not the same as Data Protection Impact Assessments (DPIAs) required under the UK GDPR. DPIAs are mandatory when your data processing activities are likely to result in high risks to the rights and freedoms of individuals.
DPIAs focus specifically on assessing and mitigating risks related to personal data, while cyber risk assessments can help address your wider business security measures, including but not limited to personal data. However, a cyber risk assessment could help with your DPIAs – for instance, insights you gain from these assessments can help you understand security controls you need to consider as part of your DPIAs to protect personal data.
How should you conduct a cyber risk assessment?
A comprehensive cyber risk assessment should involve the various steps, for example:
- Setting clear objectives for your assessment: You should define what you want to achieve with your assessment. Be specific about the scope and ensure that all stakeholders understand the goals. Clear objectives will help keep your assessment focused and ensure that you cover all necessary areas.
- Identifying your assets: You’ll need to know what data and systems you have. This will include your IT infrastructure, data flows, storage solutions, and any third-party services you rely on. Understanding your assets is crucial to understanding where you might be vulnerable to cyber attacks as a business.
- Assessing the value of your data: You should understand the importance of the data you hold. This will help you prioritise your security efforts, ensuring that your most critical data is well-protected. For example, consider what a competitor might pay for your data, the disruption a breach could cause, and the potential enforcement action from the ICO if there is a personal data breach.
- Identifying potential threats and vulnerabilities: You should look closely at where your vulnerabilities around cyber security lie. These could range from outdated software to insufficient staff training. Consider both internal and external threats, including sophisticated attacks such as phishing, and malware. Your assessment should also include reviewing third-party vendors' cyber security measures to ensure that potential risks from your supply chain are identified and mitigated.
- Prioritising key risks: You should know that not all risks are equal. Some may need your immediate action, while others might be acceptable with minimal mitigation. You should rank your risks and decide on the appropriate course of action, whether that means addressing them immediately or accepting them with caution.
- Taking action: Finally, you’ll need to implement the necessary changes to reduce your risks. This might involve updating software, changing policies, or providing additional training to your staff. You should make sure that these actions are aligned with the risks you’ve identified and that they effectively address your vulnerabilities.
Incorporating cyber insurance into your risk management strategy is also increasingly important. Insurers will often expect businesses to demonstrate robust cyber security measures before offering coverage. Business customers, particularly data controllers, may also expect your business to have comprehensive cyber security cover in place.
Integrating the results of your cyber security risk assessments into your data breach or incident response plans is also vital. This will help make sure your organisation is prepared to respond quickly and effectively to any cyber threats that arise.
How can a cyber security risk assessment help with UK GDPR compliance?
The UK GDPR’s accountability principle requires organisations to not only comply with the rules but also to evidence that compliance. This means your business must have the necessary documentation, policies, and procedures in place to show how you protect personal data and manage data protection risks.
One effective way to demonstrate compliance is through regular cyber security risk assessments. These assessments help you identify vulnerabilities in your systems, ensure that appropriate security measures are in place, and show that you are actively working to mitigate risks to personal data.
Regular assessments could help demonstrate to the ICO that you take your obligations under the UK GDPR seriously. For example, if your organisation suffers a data breach, being able to show that you conducted regular risk assessments and took appropriate steps to protect personal data may be a mitigating factor if the ICO considers any enforcement action.
Virtually every business faces the risk of a cyber attack. While no risk assessment can fully eliminate all risks, conducting regular and thorough cyber security risk assessments will help you identify vulnerabilities, implement necessary safeguards, and support your compliance with legal data security obligations under the UK GDPR.
If you'd like to learn more about how to develop and maintain a cyber security strategy that supports your legal and regulatory obligations, contact our friendly expert data protection solicitors.