Creating a robust information security policy is a key step in meeting your organisation’s data protection obligations and mitigating cyber risk.
For businesses of any size, but especially for small to medium-sized enterprises (SMEs) without in-house expertise, implementing and maintaining a comprehensive policy can be a significant challenge. A clear, well-drafted policy not only protects your data but also helps staff understand their responsibilities, respond to security incidents, and align with broader compliance objectives.
Whether you're starting from scratch or updating an existing policy, our data protection solicitors can help you build a policy that reflects your business model, operational risks and regulatory obligations, and ensures it remains a valuable and enforceable part of your broader compliance framework.
We discuss:
- What’s an information security policy?
- How does an IS policy fit into your organisation?
- What key elements could you include in the policy?
- Do you need a separate IS policy?
- Who is responsible for creating an IS policy?
- How do you implement and enforce the policy?
- How often should you review your policy?
- How can you get support with your IS policy?
What’s an information security policy?
An effective Information Security (IS) policy should be considered a framework to define policies, controls, and procedures to identify and mitigate vulnerability or risk. It is based on the three core principles of information security; confidentiality, integrity and availability.
Confidentiality – this is where only authorised users should be able to access or modify data.
Integrity – data should be maintained so that it’s impossible to modify; whether purposely or by accident.
Availability – authorised users should be able to access data easily when and where required.
Your IS policy should provide an overview as to how your organisation considers company information to be an asset and that it must be protected from unauthorised access, modification, disclosure, or destruction. It should clearly define responsibilities of those that are authorised to deal with information security at the organisation, and where staff can direct questions. Your policy may also link to other related policies or controls that may sit under a different function, but equally important and relevant to information security, such as the data breach procedure, which would usually be owned by the privacy or legal compliance function.
Your IS policy should be a living document, this should be regularly reviewed and updated, so that it can reflect any new or changing risk. It would be beneficial to inspect the living cyber security risk assessment in tandem, as this would conform any changes or reviews to the IS policy.
By alluding to the above points, your organisation would demonstrate from the outset, that it takes information security seriously.
How does an IS policy fit into your organisation?
As it’s one of the most critical policies for your organisation, it requires input from higher level management in different functions, and not just the information security team. The policy would not be created in isolation, you would need to coordinate the drafting of the policy into the whole Information Security framework.
You would first need to conduct an analysis of your organisation’s cyber security risk, such as outlined in our advice on how to reduce and manage cyber security risks, which can identify vulnerabilities and guide your next steps in line with your organisation’s risk appetite.
The outcomes of the risk assessment would allow the information security team to ensure appropriate security controls are implemented to prevent or mitigate risk in line with your organisations’ risk appetite.
Such controls may consist of a set of tools and procedures that the information security team can use to identify and recover from any security risk. This document is commonly referred to as the Incident Response Plan. A good incident response plan would ensure staff are able to respond to risk in a swift, but calm and collective manner. It may indicate the steps an organisation needs to take in light of a potential or actual breach and whether any communications need to be made either internally or to external parties.
A cyber risk assessment and an incident response plan is the minimum requirement within an Information Security framework (the list is not exhaustive). How much detail is required in your Information Security framework would be dependent on your organisation’s business model, what kind and how much data it holds, as well in which jurisdiction’s the organisation operates.
Once you have the information required, you would then begin to draft your IS policy. This policy would then conform other polices required in your organisation’s information security program, which should provide clarification and guidance for your staff.
Other policies that derive from the IS policy, may include (not an exhaustive list):
- Acceptable Use Policy
- Clean Desk Policy
- Data Breach Response Policy (this could also be part of the organisations’ data protection framework)
- Data Backup Policy
- Incident Response Policy
- Remote Access Policy
What key elements could you include in the policy?
The policy would be bespoke based on your organisation’s business model, for example, the size, nature and scope of the business. Essentially, an IS policy can be as broad or as narrow as you want it to be.
Purpose – state the purpose of the IS policy, which may be to understand your organisation’s approach to information security and be able to identify or prevent security breaches.
Objectives – it’s important to insert your organisations mission statement and the strategy it takes in maintaining the confidentiality, integrity and availability (CIA) of the company’s assets. The objectives must be set from higher level in order for it to have full impact. By setting these objectives at lower level, may allow staff to feel inclined to not take the IS policy (and its stance) that seriously.
Scope – You should consider to whom your policy applies. Consider internal and external stakeholders, third parties and suppliers. Best practice would suggest all staff to adhere to the IS policy.
Access - A company with global operations would wish to define the level of authority higher level management would have over certain information assets and systems.
Your IS policy should define how access is controlled to company data as well as your network systems, and whether multi-factor authentication is required to access the work network or servers. You should even consider physical access to the workplace, i.e., whether you have a visitors attendance log, whether there’s any CCTV, or an ID badge to access the building or offices. When staff use personal devices for work purposes, your policy should also address Bring Your Own Device (BYOD) risks, including how access is managed and the security measures required. You can find practical guidance in our article on creating a compliant Bring Your Own Device policy.
Training - You should inform employees of your security procedures, including general awareness training, to ensure they remain alert to information security risks, as emphasised in the ICO’s guidance on security and staff awareness. It should also stipulate how often training is to be provided and whether this is customised depending on staff roles or responsibilities, and whether this is provided at onboarding and or where risk has been identified.
If you require assistance in developing and delivering a training programme suitable for your business, our solicitors can help you. Learn more about our tailor-made GDPR training service.
Responsibility – you should establish who owns the IS policy and others that conform, such as the access control, and the data backup policy. This may be the Chief Information Security Officer (for cooperate or global companies) or the Head of Information Security for smaller companies. This person would have ultimate responsibility to ensure it’s kept up to date and in line with the organisation’s risk assessment and the business continuity plan (BCP).
Communication – you should explain how your staff will be informed about this policy and whether any cyber security awareness is endorsed at the organisation, and how.
Reporting breaches – staff should be informed how to report actual or potential security breaches and be taken to the data breach reporting procedure.
Our lawyers will work with you in developing and drafting a customised IS policy, suited to your business needs and requirements. Let us, meet your compliance goals and help you develop standards that fit around your business model and risk appetite.
Do you need a separate IS policy?
This is really a matter for your organisation and where your other compliance policies are kept. Many organisations require all policies to appear within the company’s code of conduct under relevant sub sections. This can ensure staff have one point of reference for policies for easier access. However, the downside is, that usually benefits policies mainly get looked at, as these would concern the employee more than, an IS policy.
In this day and age, where many organisations’ use Microsoft Office 365, you may feel compliance policies such as the IS or Data Protection policy should sit within the company’s intranet, where they are readily accessible, rather than scrolling through the whole code of conduct.
Your compliance policies are those that are put into place in order to comply with laws and regulations, such as those under the UK GDPR and Data Protection Act, and to sustain the organisation’s reputation. It would be understandable to have these at the forefront for not only accessibility but also for the sake of raising awareness.
Who is responsible for creating an IS policy?
Functions such as Risk Management, Compliance, Legal, Information Security, Facilities and or the Data Privacy departments, to name a few, would likely be required to assist in drafting an IS policy. Each function has their part to play when determining risk and how to prevent or mitigate it. The functions would consist of management that have a say in the decision-making process in the operational side of the business as well as, any those that have any impact. The person that has ultimate responsibility would likely be the highest level of management within the information security function.
How do you implement and enforce the policy?
This comes down to creating awareness and educating staff. A good message is always delivered from the top, we can agree that communication from management is linked to business strategy. However, the delivery of the message must be effective in order for it to have maximum impact. You should ensure the policy is accessible at all times by publishing it onto your company intranet and or provide hard copies, as well as have a system where staff are informed whenever there are updates. Lastly, for accountability, you should ask staff to confirm they have read and understood the IS policy.
How often should you review your policy?
The IS policy should be kept under continuous review. Whilst many other compliance policies are usually reviewed at least every 12 months, an IS policy should reflect any updates to the organisation’s cyber risk, which can occur at any time.
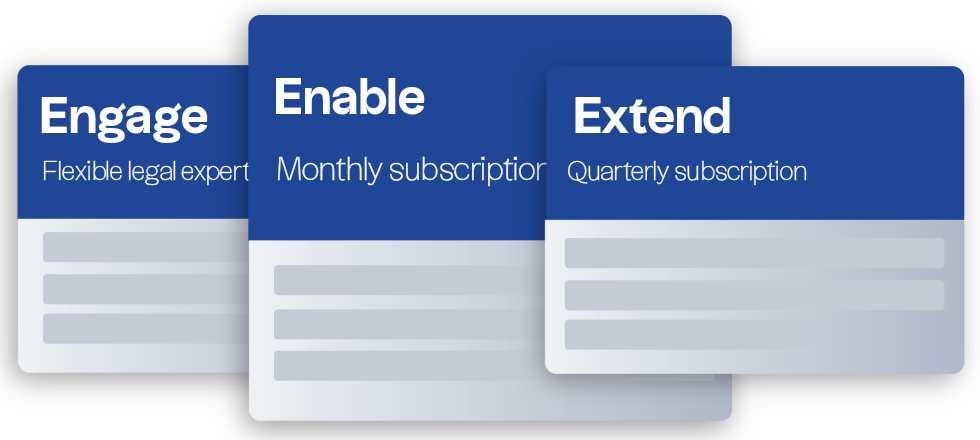
How can you get support with your IS policy?
An information security policy is more than just a compliance box-tick – it’s a living part of your business infrastructure that should evolve as your risk landscape changes. From reviewing your current approach and developing bespoke frameworks to integrating the policy across your business, our data protection solicitors can guide you through the process with practical legal support. Whether you need help drafting your first policy, updating your existing one, or training staff on best practices, we’ll work alongside you to strengthen your information governance and ensure it meets both legal standards and business priorities.